GWN Router Configuration File Tool
Product Information
| Product | Router Configuration File Tool |
|---|---|
| Manufacturer | Grandstream Networks Inc. |
| Version | 1.1.1 |
| Date | 2023/6/23 |
Product Usage Instructions
Process of Modifying Configuration File
- Export the configuration file from the web of the device.
- Use this tool to decrypt the configuration file.
- Modify the decrypted configuration file.
- Use this tool to encrypt and generate a new configuration
file. - Import the new configuration file to the device.
Usage in Linux
Decryption
Command:
./gscfgtool -t TYPE -f INTPUT-FILE -d TYPE:
Type:
Router product model: GWN7062, GWN7052, GWN7052F, GWN7001,
GWN7002, GWN7003.
INTPUT-FILE:
Exported configuration file.
Example of successful decryption in Linux:

Usage in Windows
Decryption
Command:
./gscfgtool -t TYPE -f INTPUT-FILE -d TYPE:
Type:
Router product model: GWN7062, GWN7052, GWN7052F, GWN7001,
GWN7002, GWN7003.
INTPUT-FILE:
Exported configuration file.
Example of successful decryption in
Windows:

Grandstream Networks Inc.
Router Configuration File Tool User Guide
Version: 1.1.1 Date: 2023/6/23
Table of Contents
PROCESS OF MODIFYING CONFIGURATION FILE ……………………………………………. 4 USAGE IN LINUX …………………………………………………………………………………………….. 5
Decryption ………………………………………………………………………………………………………………………………. 5 Command ……………………………………………………………………………………………………………………………. 5 Note ……………………………………………………………………………………………………………………………………. 6
Encryption……………………………………………………………………………………………………………………………….. 6 Command ……………………………………………………………………………………………………………………………. 6 Note ……………………………………………………………………………………………………………………………………. 9
USAGE IN WINDOWS …………………………………………………………………………………….. 10
Decryption …………………………………………………………………………………………………………………………….. 10 Command ………………………………………………………………………………………………………………………….. 10 Note ………………………………………………………………………………………………………………………………….. 11
Encryption……………………………………………………………………………………………………………………………… 11 Command ………………………………………………………………………………………………………………………….. 11 Note ………………………………………………………………………………………………………………………………….. 13
Page | 2
Table of Figures
Figure 1 : Example of successful decryption in Linux ……………………………………………………………………….. 5 Figure 2 : Example of decryption failure in Linux (using wrong type) ………………………………………………….. 6 Figure 3 : Example of successful encryption in Linux ……………………………………………………………………….. 8 Figure 4 : Example of encryption failure in Linux (missing “www/” directory) ……………………………………….. 8 Figure 5 : Example of successful decryption in Windows ………………………………………………………………… 10 Figure 6 : Example of decryption failure in Windows(using wrong type) ……………………………………………. 11 Figure 7 : Example of successful encryption in Windows………………………………………………………………… 12 Figure 8 : Example of encryption failure in Windows(missing “www/” directory) …………………………………. 13
Table of Tables
Page | 3
PROCESS OF MODIFYING CONFIGURATION FILE
1Export the configuration file from the web of the device; 2Use this tool to decrypt the configuration file; 3Modify the decrypted configuration file; 4Use this tool to encrypt and generate a new configuration file; 5Import the new configuration file to the device.
Page | 4
USAGE IN LINUX
Decryption
Command
./gscfgtool -t TYPE -f INTPUT-FILE -d TYPE:
Router product model: GWN7062, GWN7052, GWN7052F, GWN7001, GWN7002, GWN7003. INTPUT-FILE:
Exported configuration file.
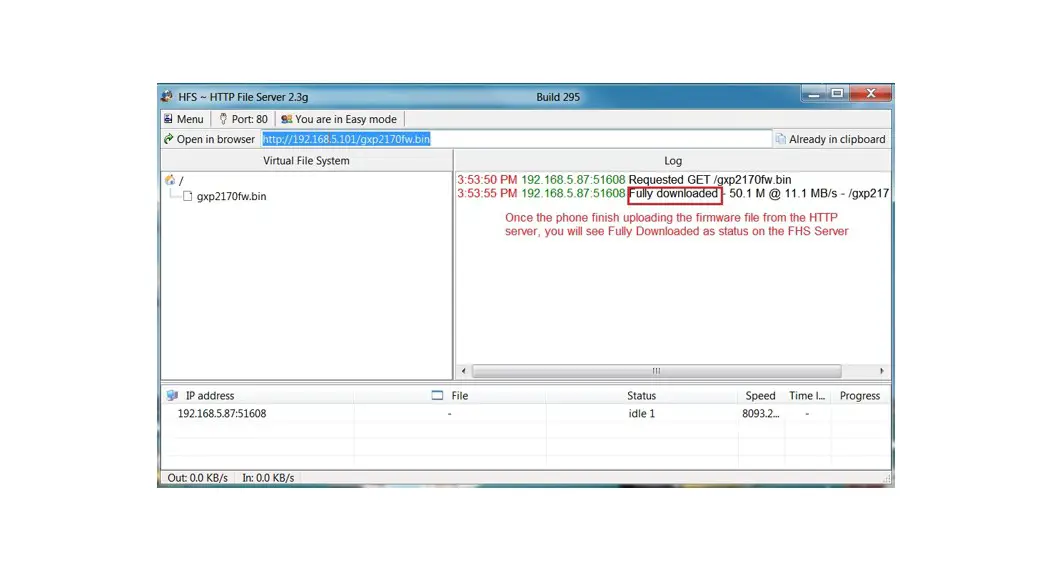
Figure 1: Example of successful decryption in Linux
Page | 5
Figure 2: Example of decryption failure in Linux (using wrong type)
Note
1The decrypted configuration file will be stored in the program running directory, see “data/”, “etc/config/”, “www/”, “tmp/”.
Encryption
Command
./gscfgtool -t TYPE -f INTPUT-FILE -e TYPE:
Router product model: GWN7062, GWN7052, GWN7052F, GWN7001, GWN7002, GWN7003. OUTPUT-FILE:
New configuration file.
Page | 6
Page | 7
Figure 3: Example of successful encryption in Linux
Figure 4: Example of encryption failure in Linux (missing “www/” directory)
Page | 8
Note
1The program running directory needs four directories “data/”, “etc/config/”, “www/” and “tmp/” to generate configuration file.
Page | 9
USAGE IN WINDOWS
Decryption
Command
gscfgtool.exe -t TYPE -f INTPUT-FILE -d TYPE:
Router product model: GWN7062, GWN7052, GWN7052F, GWN7001, GWN7002, GWN7003. INTPUT-FILE:
Exported configuration file.
Figure 5: Example of successful decryption in Windows
P a g e | 10
Figure 6: Example of decryption failure in Windows(using wrong type)
Note
1The decrypted configuration file will be stored in the program running directory, see “data/”, “etc/config/”, “www/”, “tmp/”;
2″gscfgtool.exe” depends on “7z.exe” and “7z.dll”, which we have provided. If the “7z.exe” we provided doesn’t work properly or you want a newer version, you can download it from “https://www.7zip.org/”;
3Note that “7z.exe” and “7z.dll” must be in the same directory as “gscfgtool.exe” or in any directory specified by the environment variable “PATH”.
Encryption
Command
gscfgtool.exe -t TYPE -f OUTPUT-FILE -e TYPE:
Router product model: GWN7062, GWN7052, GWN7052F, GWN7001, GWN7002, GWN7003. OUTPUT-FILE:
New configuration file.
P a g e | 11
Figure 7: Example of successful encryption in Windows
P a g e | 12
Figure 8: Example of encryption failure in Windows(missing “www/” directory)
Note
1The program running directory needs four directories “data/”, “etc/config/”, “www/” and “tmp/” to generate configuration file;
2″gscfgtool.exe” depends on “7z.exe” and “7z.dll”, which we have provided. If the “7z.exe” we provided doesn’t work properly or you want a newer version, you can download it from “https://www.7zip.org/”;
3Note that “7z.exe” and “7z.dll” must be in the same directory as “gscfgtool.exe” or in any directory specified by the environment variable “PATH”.
P a g e | 13